Identity and the Login: Who Owns "Who's That?"
Tim Clissold's Mr. China is a memoir about running a buyout fund in China in the early 90s. The main plot of the book is that the investments lose money, but they lose it in two ways:
- The fund buys a business that looks profitable, and while the business keeps growing, margins aren't great. Eventually, it turns out that someone is stealing the money by taking kickbacks or embezzling funds.
- The fund buys a business that looks profitable, and is profitable. The business grows for a while, until one day the manager stops answering his phone and suddenly all the money has been transferred to an offshore bank account.
The mechanism for that second maneuver is the company chop, a stamp that allows the holder to do business as the company. Holding on to the chop as a way to retain control of the company still comes up from time to time, and it raises all sorts of interesting questions. A company is a legal means to coordinate behavior—a way to treat a group of people, assets, and contracts as if it's just one person. But this means that it needs some way to verify who is entitled to act on the company's behalf and under what circumstances. This is a top-to-bottom question at every company; Starbucks needs to know when a barista can give you a free replacement for a drink you spilled without asking their manager, and Starbucks also needs to decide what kinds of strategic choices the CEO can make without getting permission from the board.
As with so many other human problems, this is expressed most explicitly in software, where vague norms and qualitative understandings have to give way to yes-or-no rules. Modern identity products are a sort of anti-product, since what they're selling is an alternative to passwords as they're currently used. Un-managed passwords are a mess, because the options people have are:
- Reusing passwords.
- Creating easy-to-memorize passwords (fine at small scale, but you're not going to keep fifty iterations of correct horse battery staple in your head).
- Forgetting passwords—which, as it turns out, often means giving up on a service because logging in is too annoying.
There are, naturally, alternatives to this, and some of them are driving significant economic value:
- One of the easiest is authentication over email. Instead of building a secure and convenient login system, a site can just outsource the security and ubiquity to Gmail and Outlook. This works for some applications, like Substack (if you try to leave a comment while in an incognito window, you'll be prompted to enter your email, then emailed a one-click login). Slack does something similar. And Blind takes the authentication one step further: you can comment anonymously, but with your employer disclosed, if you use a corporate email address.
- Password managers let users store multiple passwords locked behind a single master password. 1Password has raised a total of $300m, and Dashlane has raised $211m.
- Transmit Security, which offers biometric login solutions, has raised $583m.
- On the corporate identity side, ForgeRock just went public with a $4bn enterprise value, and Okta's market cap is $38bn.
- Years ago, Ben Thompson wrote about how much Microsoft's enterprise sales model relied on controlling permissions through Active Directory, and what a threat Okta was to this ($). Microsoft is still working on this, and recently announced that the passwordless future is here: "Use the Microsoft Authenticator app, Windows Hello, a security key, or a verification code sent to your phone or email to sign in to your favorite apps and services..." Meanwhile, Google generates and saves passwords in Chrome, and has an authenticator app; iOS also generates and saves passwords. And smaller enterprises are competing in this area, too; Dropbox has a free password manager, too.
- Since Apple controls its hardware and has a fair amount of control over software, too, it can also push biometrics. I log in to my phone with my face and my computer with my fingerprint. It's convenient.
- While passwords for logging in are important, there's an adjacent area of identity that's also getting interesting: verifying real names during the initial setup of a consumer product, especially in consumer finance, and identity re-verification for hijacked accounts. Stripe Identity offers this.
Clearly, many companies view identity as an important topic. In each case, the real question is mapping a digital identity to a real one, since digital identities are basically free but real identities are scarce—and, more grimly, because it's hard to punish a digital identity by doing anything beyond deleting an account, whereas a real-world person who uses an digital identity to misbehave can get in legal trouble.
Part of the reason these products proliferate is that asking users to create a username and password is a cheap default for most companies, but it imposes a negative externality: every additional password is a hit to usability (since it means more to remember) or security (if it's being reused). Companies typically don't notice negative externalities until they're faced with the costs, but once they see them, they try to solve them.
For Microsoft and Google (and, for that matter, Stripe), the upside from low-friction security is obvious: a bigger software economy will end up benefiting them, since it probably means more Microsoft product subscribers (and, increasingly, more Azure usage), more clicks on search ads, and more transactions. For Okta, the answer is a little more vague, but one intriguing point comes from their most recent investor day:
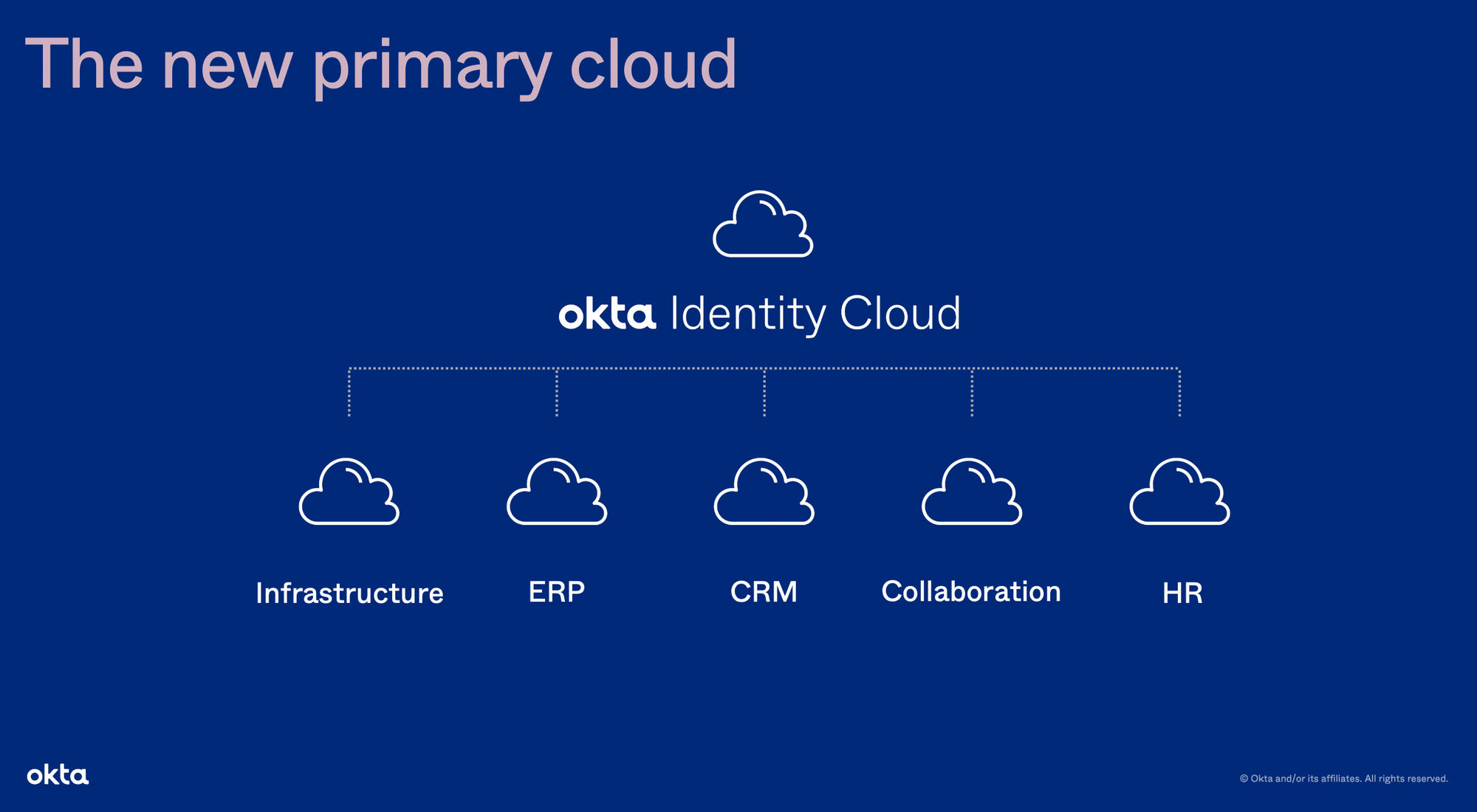
Several $10bn+/year businesses are directly downstream from identity. Okta's plan is not to leverage this to control those downstream products, but it will be able to affect them: since Okta is managing a consistent identity across products, a) it has a decent start on sharing data between them, and b) it's a way to get analytics on what people actually use. One driver of the high lifetime value of enterprise software contracts is inertia: cancelling is a choice, and keeping a product that's already in the budget "just in case" is a decision people often make when spending their own money. It would be interesting to someday calculate just how much SaaS revenue, and thus how much SaaS market cap, is made up of empty seats that still generate ARR, or of add-ons that got purchased because they seemed like a good idea and haven't quite gotten used yet. In the very long term, SaaS companies don't want to make their money this way, since it means a) making money at the expense of customers, and b) selecting for customers whose operational deficiencies will eventually prevent them from growing and producing more revenue. But in the short term, the incentives are weak. Okta's incentives, on the other hand, are quite strong: if they can identify software that's being paid for but not used, they can show customers a very high return on using Okta, and that locks them in.
So, in this case, the upside for an identity management business is that it both upgrades the rest of the customer's software stack and makes the identity product more indispensable. And, returning the customer-quality point, it means that those customers will have a leaner cost structure and higher growth rates.
Meanwhile, identity in general contributes to the "stolen corporate chop" problem raised above. One of the ways a big company creates value is that it gives individual workers on-demand access to teammates and capital they couldn't get on their own. This is straight out of Ronald Coase's explanation for why there's such a thing as an airline, instead of a series of one-off chartered flights with freelance pilots—it is simply cheaper to bundle more people and capital into a single economic entity that can transact within itself at low cost.1 But those low transaction costs apply to good people as well as bad, and they apply to both the use and misuse of company assets. More software products mean more vectors for hacks; vulnerabilities in SolarWinds produced many downstream problems, and got identified because the hackers tried to set up multifactor authentication for a compromised FireEye account on a new device. Managing identity is high-risk, because to hackers it's high-reward; once they have a user's identity, they are, for many corporate purposes, equivalent to that user, and can bootstrap from there to get more access.2
So what identity management ends up doing, for both enterprises and consumers, is solving the vendor consolidation problem. There are many software providers who solve particular business problems, and it's easy to accumulate subscriptions both as a consumer and as a company. But that also means accumulating costs, and risks. The endgame for identity management is to centralize those risks in one place, and to turn that from a kind of insurance or convenience into a high-return decision by also centralizing costs the same way. Choosing one company to manage all of your identity and login decisions will increasingly be the default, and that company will have many ways to take advantage of its status as the mediator between who you are in the real world and how that’s recognized in the digital one.
A Word From Our Sponsors
Over 78% of funds either use or expect to use alternative data to outperform other funds or support the risk management process. Unfortunately, the majority of that data is unstructured.
Turning that unstructured data into insight takes a data team, custom NLP models, and months to train them.
Or you could use Accern to quickly deploy AI models pre-trained for financial use cases - from credit risk, to ESG, to deal sourcing.
Select your data sources, pick the themes and companies you want to track, select your model, and get data directly to your dashboard - no coding required. Diff readers get a free one-month trial - learn more below!
Elsewhere
Facebook Apologetics
A long time ago, the Internet seemed to consist of about 90% debates over creationism and around 10% everything else. It was an interesting time. These debates had variable levels of quality, so they ended up being a nice laboratory for learning rhetorical tricks and fallacies. (This was not limited to one side—the nature of flamewars is that the discussion goes on longest if it’s between two people who keep saying easily refuted things to one another, so no matter the topic, the median piece of flamewar content is going to be mistaken even if one side is actually correct about the big picture.) One memorable point that came up was on intermediate species: if there are two living species that are similar to one another, evolution implies a common ancestor, and if we can't find the common ancestor, that scores one point against evolution. But the pro-evolution side pointed out that if we do find a common ancestor, we're now missing two intermediate species—something halfway between each of the current ones and the halfway-between common ancestor. So that critique ends up being uninformative because it gets quantitatively stronger every time a specific instance gets refuted.
Something similar is happening with Facebook and moderation. In the bad old days, Facebook's moderation was opaque, and it was easy to say that they didn't tell us what the rules were. Now, the company is opening up more about its processes, and, as a result, there are more specific ways to talk about the company being opaque:
There’s still plenty that the guidelines, which Facebook has mostly confirmed in various reports over the years but is just now publishing for the first time in one place, don’t say. They don’t detail exactly how a demotion works and exactly how much it reduces a piece of content’s reach. Or how severely a certain kind of post, like a link to spam, is throttled in the News Feed relative to a post about health misinformation, for example.
The tradeoff at the other end is that when Facebook does open up about all its moderation rules. When they do that (as happened, for example, in 2018), people find all sorts of fun edge cases. The rules will always have edge cases, and making the rules explicit makes it easier to take advantage of those edge cases, so transparency ends up selecting for content that violates the spirit of the law but adheres to the letter of the law. It is, as Facebook demonstrates, very hard to moderate a global forum—and it's even harder to moderate it while making moderation decisions in public.
Food Delivery and Unit Economics
New York has passed stricter laws on food delivery, setting minimum per-trip payments, giving workers some control over routes, and letting them use restaurants' restrooms. Of the large companies contacted for comment, Uber declined to say anything, Doordash put out a neutral statement, and GrubHub was positive:
These bills are common-sense steps to support the delivery workers who work hard every day for New York’s restaurants and residents,” according to a statement from Grant Klinzman, a Grubhub spokesperson. “Ensuring they receive a living wage and have access to restrooms isn’t just a good idea -- it’s the right thing to do."
Some of this is probably because they don't have any realistic chance of changing the law, whether they like it or not, but these rules do tend to help the biggest players relative to everyone else. If there's an additional fixed cost to running a delivery network, that's a tax for the networks that run below capacity, but—since these companies are all hiring workers out of a fairly liquid labor market—an indirect subsidy to the companies that can keep utilization high, and have enough orders that they can route people to minimize the impact of a per-order minimum. The bill only covers third-party delivery services, so restaurants themselves will be able to pay delivery workers on different terms, but if the big platforms are required to give workers a higher minimum income, it's not clear that those restaurants will be able to.
More Air Taxis
A few weeks ago I wrote about how United Airlines' orders for supersonic planes and air taxis are a way to take the strategy of hub-and-spoke systems seriously. They are not the only ones, though; Gol, a low-cost carrier in Brazil, is also ordering air taxis ($, FT). They hope to get their fares "down to the equivalent of an Uber ride," a testament to both their ambition and to how much Uber and Lyft prices have been rising. Commuting in three dimensions makes a lot more sense as a way to deliver high-value connecting traffic on high incremental margin flights, but it can work more broadly, too.
Business and China
The FT highlights a collapsed buyout deal between Blackstone and a Chinese real estate company as further evidence that investment in China is getting harder ($). It is striking. Schwartzman funded the Schwarzman Scholars program, which very much looks like a way for a forward-thinking investor to develop deeper connections to China. In one sense, though, it's a positive sign: the most cynical reading of China's economic policies is that proximity to the CCP is the only determinant of success, and if Blackstone can't close a deal, it's at least evidence that the cause is a policy change, and not an attempt to reward insiders and punish outsiders.
Coase's work almost feels redundant, since he explains a hypothetical that most people don't wonder about. But while it's obvious that companies exist, Coase was able to look at the question with fresh eyes and make it obvious why. ↩
This kind of identity bootstrapping occurs in the analog world, too. At one point in the collapse of the law firm Dreier LLP, Marc Dreier took one meeting with an outside lawyer, pocketed his business card, then impersonated the same lawyer at his next meeting by using the business card as a prop. ↩